Audit Preparation
Conduct self-assessments to benchmark current maturity against established internal controls and external regulatory frameworks.
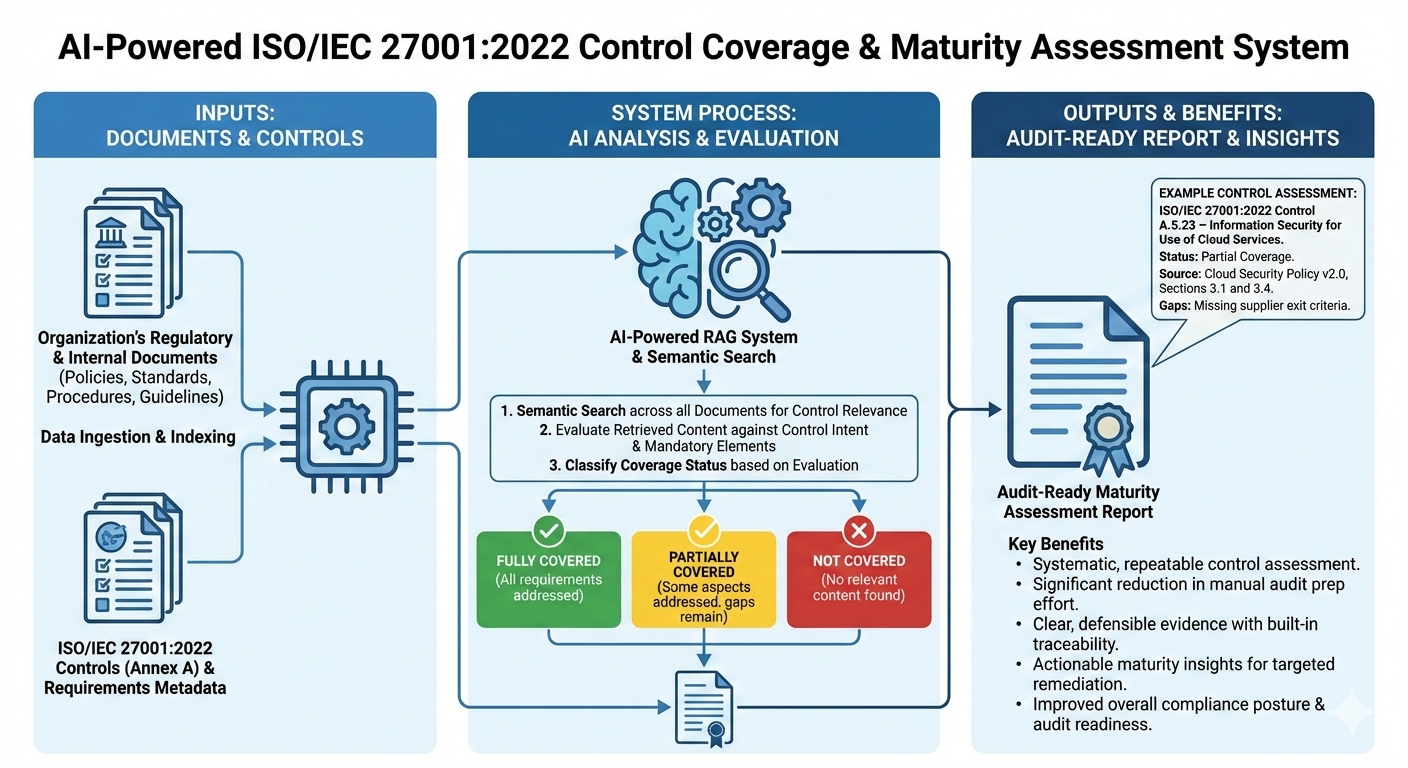
Regulatory Control Coverage Assessment for Audit Readiness
The systematic assessment of documentation against control requirements, a core component of maturity assessments and audit preparation, allows for rapid benchmarking against established internal and external frameworks and streamlines audit preparedness by automating gap identification for a transparent review process.
Scenario:
An Information Security Manager is preparing for an ISO/IEC 27001 certification audit and need to determine to what extent the existing regulatory and internal policy documents cover each ISO/IEC 27001:2022 control. For every control, it should be identified whether the control it is fully covered, partially covered, or not covered. The system should generate an audit-ready maturity assessment report.
System Process:
The system ingests and indexes all regulatory and internal documents (e.g., corporate policies, standards, procedures, guidelines) and the complete set of ISO/IEC 27001:2022 control requirements (Annex A).
For each ISO/IEC 27001 control, the RAG system semantically searches across all documents to locate relevant sections, clauses, or statements and evaluates the retrieved content against the control’s intent and mandatory elements. It pre-classifies the result for each control as:
- Fully Covered – All control requirements are explicitly addressed.
- Partially Covered – Some aspects are addressed, but gaps or ambiguities remain.
- Not Covered – No relevant content is found.
and generates a structured control-by-control assessment report including coverage status, a summary of evidence found and the identified gaps or weaknesses (if any).
Traceability:
Each control assessment is supported with precise references, for example:
“ISO/IEC 27001:2022 Control A.5.23 – Information Security for Use of Cloud Services”
“Source: Cloud Security Policy v2.0, Sections 3.1 and 3.4 (Partial Coverage – missing supplier exit criteria).”
Benefit:
Systematic, repeatable control assessment across an entire regulatory framework.
Significant reduction in audit preparation effort, replacing manual control mapping with automated analysis.
Clear, defensible evidence for auditors through built-in traceability.
Actionable maturity insights, enabling targeted remediation before formal audits and improving overall compliance posture.
Control Gap Analysis and Cross-Mapping
This scenario highlights the RAG system’s ability to act as a Gaps Finder by comparing internal policy against external regulatory requirements, a core component of any maturity assessment.
Scenario:
A Compliance Manager asks:
“Identify all instances where our internal ‘Vendor Risk Management Policy’ fails to explicitly mention a required control from both ISO 27001 (Control A.15.1.2) and the latest NIST Cybersecurity Framework (Subcategory ID.RA-1.1), and suggest the necessary policy update text.”
System Process:
The system instantly searches and retrieves:
- The entire Internal Vendor Risk Management Policy
- The text of ISO 27001:2022 Control A.15.1.2 (Addressing Security in Supplier Agreements).
- The text of NIST CSF Subcategory ID.RA-1.1 (Identification of asset vulnerabilities). and uses semantic analysis to compare the retrieved documents. It then generates a gap analysis report containing:
Outcome:
- Identified Gap: The Internal Policy only mandates “annual review” but lacks a procedure for “continuous monitoring and re-assessment upon security incident,” which is required by NIST ID.RA-1.1.
- Suggested Text: Provides a paragraph of natural language text to be inserted into the policy that closes the control gap, citing both external standards.
- Traceability: The response is instantly accompanied by source citations (e.g., “Source: Internal Policy V.3.1, Paragraph 4.2-A (Missing Element); NIST CSF, ID.RA-1.1 (Required Action); ISO 27001:2022 A.15.1.2 (Context)”).
Benefit:
Automated, objective identification of control gaps. Converts a manual cross-referencing task into a single query, ensuring the organization’s policies are aligned with multiple regulatory standards before the auditor arrives.
Stay in the Loop
Just drop us a line and we'll be in touch to update you on the latest developments and availability.